Introducing Olivier: CloudThinker's SuperPower Security Agent for Cloud
I've spent over a decade building and securing cloud infrastructure — from startups shipping their first container to enterprises managing thousands of workloads across multi-account AWS environments. I've been the engineer at 2:47 AM triaging GuardDuty alerts. I've been the one writing 80-page compliance reports by hand. I've watched teams burn out not because they lacked talent, but because the tooling demanded too much of them.
The problem was never the people. It was the model.
Every security tool I used followed the same pattern: scan, generate a list of findings, hand it to a human. The human then had to figure out what's critical, what's noise, how it maps to compliance, and what to actually do about it. That mental overhead — the context-switching, the cross-referencing, the tribal knowledge that lives in one person's head — that's what breaks teams.
So we built something different.
Your cloud runs 24/7. Your security engineer should too.
Meet Olivier
Olivier is CloudThinker's agentic Security Engineer — an AI agent with 20 purpose-built security skills from CloudThinker's Skills Hub, which already offers 1000+ pre-built, composable AI skills for cloud operations.
Not a dashboard. Not a scanner. A security engineer that:
- Runs Checkov, Prowler, Trivy, and kube-bench simultaneously
- Reads CloudTrail logs and builds incident timelines automatically
- Writes the compliance report your auditor needs, with evidence attached
- Learns from every scan — each finding strengthens future prevention
I've worked with security teams across dozens of organizations. The pattern is always the same: skilled engineers drowning in alerts, spending 70% of their time on toil that should be automated. Olivier doesn't replace those engineers — it gives them back their time so they can focus on architecture, threat modeling, and the decisions that actually require human judgment.
How It Works
Here's what I learned after years of integrating security tools: the problem isn't any single tool. Checkov is excellent at IaC scanning. Prowler is excellent at cloud posture. Trivy is excellent at container CVEs. The problem is orchestration — knowing which tools to run, in what order, and how to connect their outputs into a coherent picture.
That's exactly what Olivier does. Each of the 20 security skills is a self-contained capability — with its own tools, instructions, and domain knowledge — that Olivier orchestrates based on what you ask.
One prompt. Multiple skills. Complete coverage.
When you say "Scan our EKS clusters for CIS compliance", Olivier activates kube-bench, CIS benchmark, admission control review, and network policy audit in parallel. When you say "We got a GuardDuty alert", Olivier chains detection → forensics → containment → timeline automatically.
The skills aren't isolated scanners. They share context through CloudThinker's knowledge graph — so IAM findings inform network policy, GuardDuty alerts trigger CloudTrail forensics, and incident timelines feed back into prevention rules. This is the kind of cross-domain reasoning that used to live exclusively in the head of your most senior security engineer. Now it's codified and always on.
Real Output: Kubernetes Security Assessment
One prompt — "Scan helm security issues and build SOC compliant dashboard" — produces this:
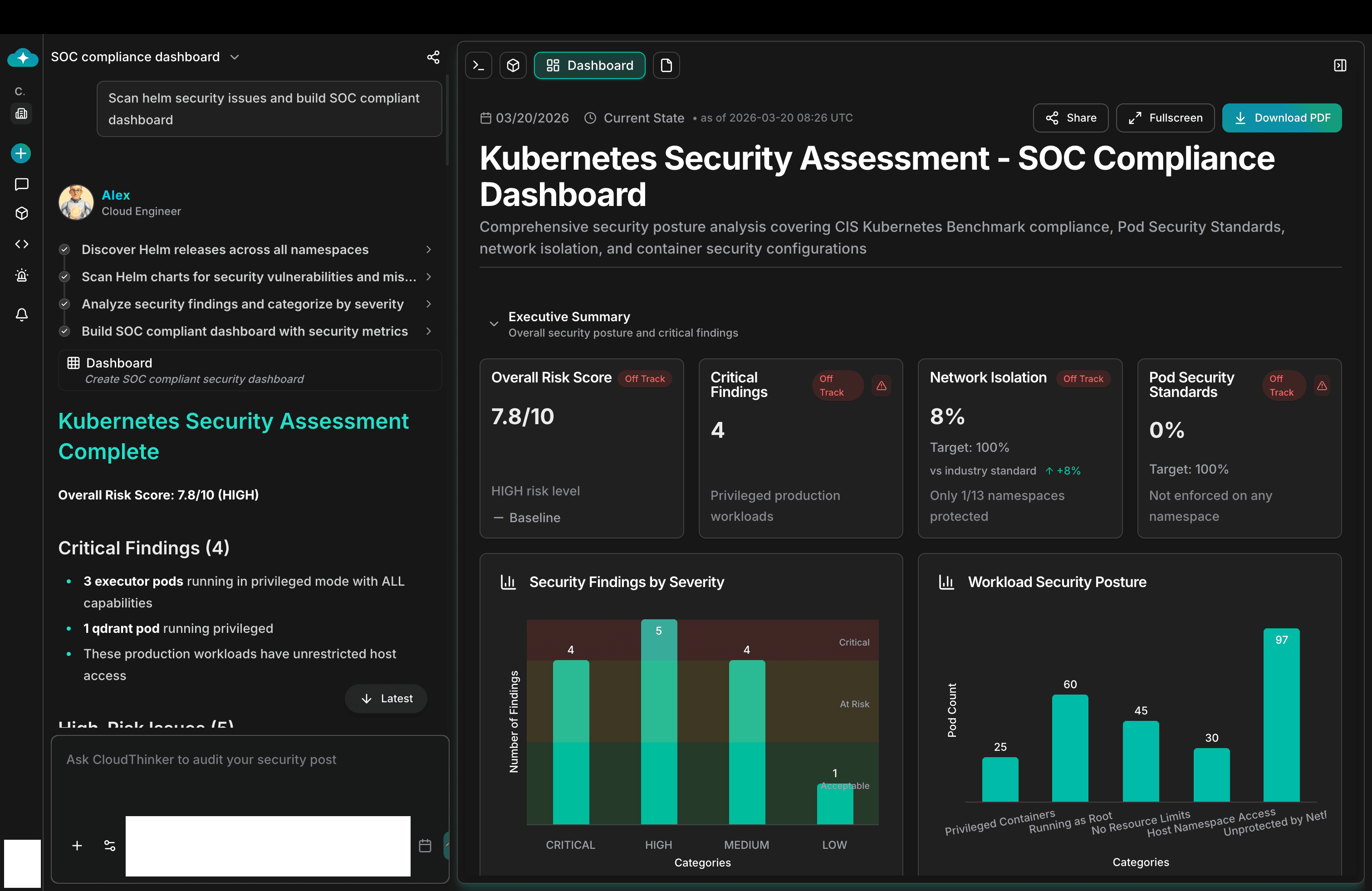
Kubernetes Security Assessment — SOC Compliance Dashboard with Overall Risk Score 7.8/10, 4 Critical Findings, Network Isolation at 8%, Security Findings by Severity
I've seen consultants charge $30K–$50K for an assessment that delivers less than what Olivier produces in minutes. Not because the consultants aren't good — but because a human can only hold so much context at once. Olivier doesn't forget. It doesn't get fatigued at 3 AM. And it doesn't charge by the hour.
Traditional Assessment
$15K–$50Kper engagement
- 2–4 weeks consultant engagement
- Point-in-time snapshot — stale by next deploy
- Manual dashboard setup
- Quarterly cadence at best
Olivier Security Scan
A few dollarsper scan
- Full assessment in minutes
- Always current — reflects live state
- Interactive dashboard auto-generated
- Continuous — every PR or on-demand
20 Skills. Three Domains. One Agent.
When I designed Olivier's skill set, I drew from every security engagement I've led. The question wasn't "what tools exist?" — it was "what does a senior security engineer actually do day-to-day, and what keeps them up at night?"
The answer organized naturally into three domains: Prevention (stop bad things before they deploy), Detection & Response (catch and contain what gets through), and Compliance (prove to auditors that you're doing both).
Most teams start with prevention — IaC scanning, CSPM, secrets detection. That alone eliminates the majority of misconfigurations before they reach production. As your security posture matures, you layer in detection and compliance. The skills compose automatically — a GuardDuty alert triggers CloudTrail forensics, which feeds the incident timeline, which maps to compliance controls.
You don't configure 20 tools. You tell one agent what you need.
Prevention
IaC Scan (Checkov)
CSPM (Prowler)
Container (Trivy)
K8s Hardening (kube-bench)
K8s Admission (OPA)
Secrets (TruffleHog)
IAM Least-Privilege
IAM Escalation
Network/SG Audit
TLS Audit
CI/CD Security
Vuln Prioritization
Detection & Response
Threat Detection (GuardDuty)
Forensics (CloudTrail)
IR Containment
IR Timeline Builder
Compliance
CIS Benchmark
Policy-as-Code (OPA/Rego)
Encryption Audit
Data Classification
Cloud Posture (Prowler)
Every skill is available in the Skills Hub — browse, activate, and customize for your environment.
How It Extends
This is where it gets interesting — and why I call Olivier a superpower rather than just a product.
In every organization I've worked with, the hardest security problems aren't generic. They're specific: your compliance framework, your incident response runbook, your escalation paths, your internal tooling. Off-the-shelf security products can't encode that institutional knowledge. So it stays in people's heads, in outdated wiki pages, in Slack threads nobody can find.
Olivier's 20 security skills are just the starting point. CloudThinker's Skills Hub already offers 1000+ pre-built, composable skills spanning observability (Datadog, Prometheus, Grafana), databases (PostgreSQL, MongoDB, Redis), CI/CD (GitLab, GitHub, Jenkins, Terraform), Kubernetes (ArgoCD, EKS, GKE), cost optimization, and more. Olivier's security skills are built on the same open architecture — which means:
-
Compose across domains — Chain security skills with operational skills: "On every PR, run IaC scan + secrets detection + least-privilege check, then post results to Slack via the SlackOps skill."
-
Custom compliance frameworks — Encode your organization's specific security policies as skills that Olivier enforces automatically alongside the built-in 1000+.
-
Team-specific runbooks — Turn your incident response procedures, escalation paths, and remediation playbooks into skills. I've seen teams convert 20-page IR playbooks into skills in an afternoon. The same pattern used by the built-in deployment checklists and DNS cutover skills in the Hub.
-
New tool integrations — Wrap any security tool (your own scripts, third-party scanners, internal APIs) as a skill. The same way the Hub integrates Checkov, Prowler, Snyk, tfsec, Trivy, and Kubescape.
Build Your Own in Minutes
CloudThinker's Skills Framework makes it simple. A Skill is a declarative SKILL.md file — define the trigger patterns, required tools, guardrails, and output schema. Three steps:
- Describe — Articulate the operation in plain language, or point to an existing runbook
- Generate — CloudThinker auto-generates the full
SKILL.mdwith tools, guardrails, and structured output - Deploy — Test, refine, go live. The skill is immediately available to Olivier
No code required. Your team's security knowledge becomes a reusable, governed, always-on capability — not trapped in someone's head waiting to walk out the door.
Learn how: cloudthinker.io/skills/framework · Browse 1000+ skills: cloudthinker.io/skills

CloudThinker Skills Framework — describe, generate, deploy
Why It's a Superpower
I've evaluated hundreds of security tools over my career. Most of them solve one problem well and ignore everything else. The ones that try to be platforms end up as dashboards — pretty, expensive, and disconnected from how engineers actually work.
CloudThinker is different because of three architectural decisions I made early and refused to compromise on:
1. Skills, not scripts. Each skill carries domain knowledge — not just what to scan, but why a finding matters, how to fix it, and which compliance controls it maps to. A script finds an open security group. A skill explains which services are exposed, what data flows through them, and whether it violates PCI-DSS Requirement 1.3. This is the difference between a finding and an insight.
2. Knowledge graph, not flat reports. Every finding is connected to infrastructure topology, historical incidents, and compliance frameworks. Olivier doesn't just flag 0.0.0.0/0 — it knows this security group is attached to a production RDS instance that stores PII, and that the same misconfiguration caused a P1 incident three months ago. Context is everything in security. Without it, you're just generating noise.
3. Compound learning. Every scan makes Olivier smarter. Validated findings get reinforced. False positives get deprioritized. Your team's remediation patterns become Olivier's recommendations. Over time, Olivier carries the operational context of a senior security engineer who's been on your team from the start — except it never takes PTO and it never forgets.
Getting Started
- Browse the Skills Hub — explore 1000+ pre-built skills including Olivier's 20 security capabilities
- Connect your AWS account — read access to CloudTrail, GuardDuty, IAM, security groups
- Connect your Kubernetes clusters — for EKS security scanning
- Start with one prompt — "Olivier, run a full security assessment."
The first scan typically surfaces findings hiding in plain sight — open security groups, over-permissioned IAM roles, unencrypted S3 buckets, missing CIS controls. The kind of findings that experienced security engineers know to look for, but that get missed when teams are stretched thin and moving fast.
I've seen the same pattern at every company I've worked with: the expertise exists, but the bandwidth doesn't. Olivier closes that gap.
Your cloud infrastructure runs 24/7. Your security engineer should too.
Explore the full skills library at cloudthinker.io/skills
